![PDF] Social Engineering Theory: A Model for the Appropriation of Innovations with a Case Study of the Health MDGs | Semantic Scholar PDF] Social Engineering Theory: A Model for the Appropriation of Innovations with a Case Study of the Health MDGs | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/9d52fea6d529599400f30cc2f4339b4d9fc60d46/7-Table1-1.png)
PDF] Social Engineering Theory: A Model for the Appropriation of Innovations with a Case Study of the Health MDGs | Semantic Scholar

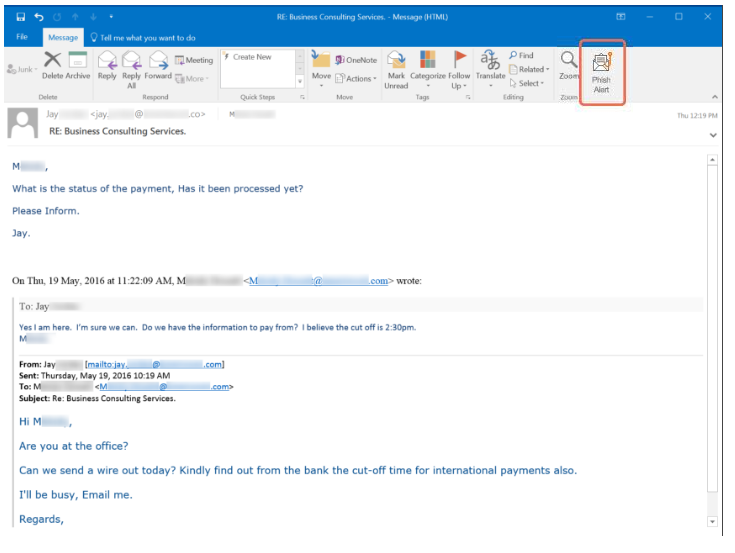
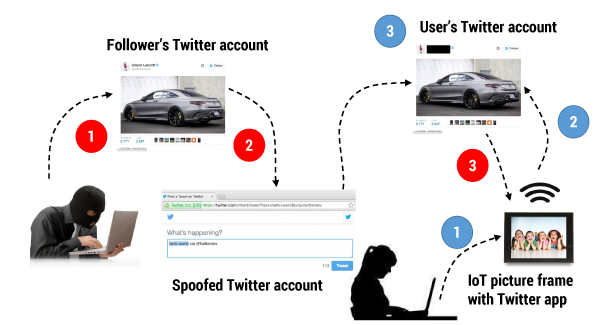
PDF) CASE STUDY ON SOCIAL ENGINEERING TECHNIQUES FOR PERSUASION | International Journal on Applications of Graph Theory in Wireless Ad hoc Networks and Sensor Networks (GRAPH-HOC) - Academia.edu